produced by chain | 1 replies
Buzzen V5 Webchat Development Announcement
err0r is actively working on the Buzzen V5 Webchat to improve performance, usability, and overall chat experience.
We welcome community feedback and feature suggestions.
If there’s something you’d like to see added, improved, or changed, please share your ideas. Your input helps shape the future of the platform.
Thank you for being part of the Buzzen community.
produced by chain | 0 replies
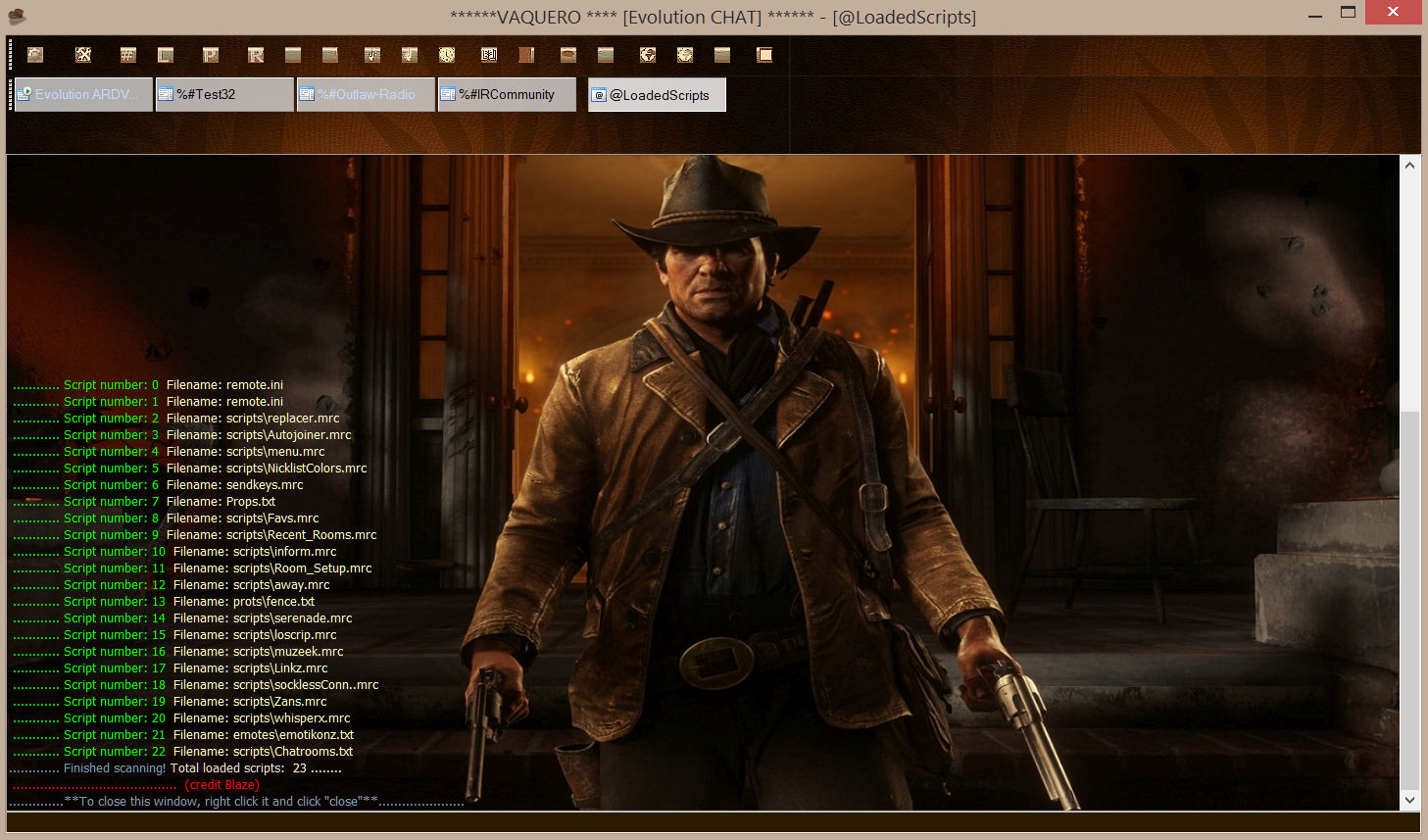
Just to let you all know deVilScript 3.0 has been releasedlooking to read more about the script please go to www.devilscript.com for more info and insights on the script 👍
produced by coders-irc_Bot | 0 replies
🎉 IRC4Fun celebrates 17 years of serving Internet Relay Chat users, internationally! 🌐 (and we hope to continue to many more!) 🎂
by Sinister
produced by coders-irc_Bot | 0 replies
Dialog Control eXtensions for mIRC
Support forum: None... Pre-Built dll's: https://github.com/twig/dcxdll/releases
This is DCX version 3.1+ & requires mIRC v7.45+
dcxdll-master.zip
produced by coders-irc_Bot | 0 replies
This is a small update that adds features and addresses a number of issues reported by users since the last release. It includes improvements, changes and fixes, including:Added support for dark mode on Windows 10/11.Fixed empty perform list entry crash bug.Fixed Options/DCC dialog radio buttons not working correctly.Added support for loading WebP image files.Fixed per server connect on startup bug.Fixed Log View dialog crash bug when loading large log files.Fixed control codes being stripped out of displayed lines in some events.Added Line shading option to Display/Options dialog that shades...