-
Posts
6036 -
Joined
-
Last visited
-
Days Won
17
chain last won the day on September 5 2023
chain had the most liked content!
About chain

- Birthday 01/26/1962
Contact Methods
-
Website URL
http://www.coders-resources.net
Profile Information
-
Gender
Male
-
Location
Montreal,Quebec
-
Interests
scripting and chatting
Recent Profile Visitors
204391 profile views
chain's Achievements
-
chain changed their profile photo
-
Added a video to some some great features Recording 2026-03-03 100428.mp4
-
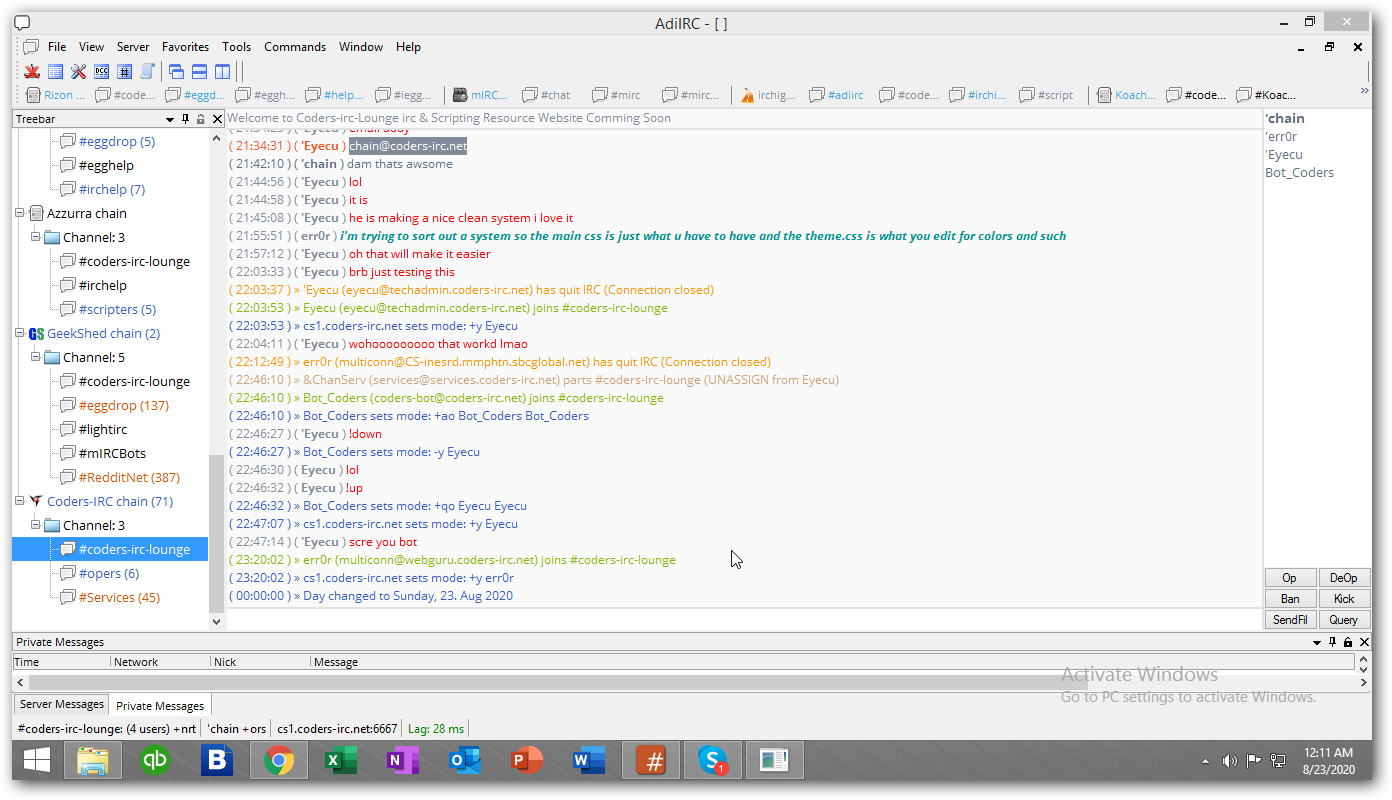
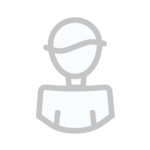
Buzzen V5 Webchat Development Announcement err0r is actively working on the Buzzen V5 Webchat to improve performance, usability, and overall chat experience. We welcome community feedback and feature suggestions. If there’s something you’d like to see added, improved, or changed, please share your ideas. Your input helps shape the future of the platform. Thank you for being part of the Buzzen community.
-
; ============================================== ; Napa182's Updated By Chain 2025 FUNNY NICK FACTS – BUZZEN READY v3 ; NO INTERNET | NO SOCKETS | WORKS 100% ; ============================================== alias -l nfact { var %nick = $1 var %gender = $2 ; === MALE FACTS === if (%gender == m) { var %facts = secretly runs a underground fight club every Friday|was once banned from 3 zoos for feeding the animals pizza|has a PhD in meme theory|can solve a Rubik's cube in 7 seconds blindfolded|once arm-wrestled a bear and won|invented the word "yeet" in 2003|has a tattoo of his own nickname in Comic Sans|can quote every Star Wars movie backwards|sleeps with a nightlight shaped like a lightsaber|believes pineapple belongs on pizza and will die on that hill } ; === FEMALE FACTS === elseif (%gender == f) { var %facts = has a secret lair under her bed full of glitter bombs|can make any outfit look like it cost $10,000|once won a staring contest with a cat|runs a black market for cute stickers|can parallel park a tank|has a playlist for every mood, including "revenge"|taught her phone to say "yas queen" on command|owns 47 shades of lipstick and named them all|can silence a room just by raising one eyebrow|once beat a GPS at navigation } ; === OTHER / NON-BINARY / NEUTRAL === else { var %facts = communicates with squirrels using only clicks|has a pet rock named Kevin and takes it on vacation|can turn any argument into a rap battle|invented a dance move called "The Glitch"|runs on caffeine, chaos, and cosmic vibes|once hacked reality with a paperclip|believes in 7 impossible things before breakfast|has a backup personality just in case|can fold a fitted sheet in under 10 seconds|speaks fluent sarcasm and emoji } ; Pick random fact & replace $1 with nick var %fact = $gettok(%facts, $rand(1, $numtok(%facts, 124)), 124) return 10@nfact: 15 $+ %nick $+ $replace(%fact, $1, 15 $+ %nick $+ ) } ; ============================================== ; TRIGGER: @nfact Nick m/f/o ; ============================================== on $*:text:/^@nfact\s+(\S+)\s+([mfo])$/iS:#: { var %nick = $regml(1) var %gender = $lower($regml(2)) var %chan = # if (%nick ison %chan) { var %fact = $nfact(%nick, %gender) msg %chan %fact } else { notice $nick Sorry, 15 $+ %nick is not in 15 $+ %chan } } ; ============================================== ; LOAD MESSAGE ; ============================================== on *:load: { echo 12 -a 15Napa182'sUpdated By Chain Funny Nick Facts v3 4(INSTANT • OFFLINE • BUZZEN READY) echo 12 -a 14Type: @nfact YourNick m (or f/o) echo -a 14,1(14,1¯15,1¯0,1¯0,1º $+ $chr(171) $+ $chr(164) $+ $chr(88) $+ $chr(167) $+ $chr(199) $+ $chr(174) $+ $chr(238) $+ $chr(254) $+ $chr(116) $+ $chr(48) $+ $chr(174) $+ $chr(167) $+ $chr(88) $+ $chr(164) $+ $chr(187) º0,1¯15,1¯14,1¯) $+ $chr(153) }
-
This feeder was made for me and then i lost a file so had to learn err0r and i've updated it. efeeder.txt
-
Im a big fan of feeders so I decided to look at what a friend did for mine and learned to make more. I made it for Buzzen Displays what new in music and artists hope you have fun with it. emusicbot.txt
-
Just to let you all know deVilScript 3.0 has been released looking to read more about the script please go to www.devilscript.com for more info and insights on the script 👍
-
> ;********************************** ;Type in /chanstats ;Make sure active window is a channel ;************************************ alias chanstats { if ($active == $chan) { var %c = $chan echo -a $str(=,50) echo -a Channel Statistics for %c / Mode: $chan(%c).mode echo -a Total Users: $nick(%c,0) / $iif($chan(%c).limit,$chan(%c).limit,No Limit Set) echo -a Op(s): $nick(%c,0,o) echo -a Halfop(s): $nick(%c,0,h) echo -a Voice(s): $nick(%c,0,v) echo -a Regular(s): $nick(%c,0,r) echo -a $str(=,50) } else { echo -a Current active window is not a channel! } } <
-
-
-
; Color Talker v1.1 - by entropy 2018 ; Only use this script on channels where you are chan op! (or you might get banned) menu channel { - Color Talker $chr(9) $+([,$iif($group(#talker).status == on,On,Off),]) .Turn $iif($group(#talker).status == on,Off,On) { $iif($group(#talker).status == on,.disable,.enable) #talker | echo -a * Color Talker is now: $iif($group(#talker).status == on,On,Off) } .- .Color $chr(9) $+([,%color,]) ..Color 00 (White) { %color = 00 | mymsg %color } ..Color 01 (Black) { %color = 01 | mymsg %color } ..Color 02 (Navy) { %color = 02 | mymsg %color } ..Color 03 (Green) { %color = 03 | mymsg %color } ..Color 04 (Red) { %color = 04 | mymsg %color } ..Color 05 (Brown) { %color = 05 | mymsg %color } ..Color 06 (Purple) { %color = 06 | mymsg %color } ..Color 07 (Orange) { %color = 07 | mymsg %color } ..Color 08 (Yellow) { %color = 08 | mymsg %color } ..Color 09 (Light Green) { %color = 09 | mymsg %color } ..Color 10 (Teal) { %color = 10 | mymsg %color } ..Color 11 (Light Blue) { %color = 11 | mymsg %color } ..Color 12 (Blue) { %color = 12 | mymsg %color } ..Color 13 (Pink) { %color = 13 | mymsg %color } ..Color 14 (Dark Grey) { %color = 14 | mymsg %color } ..Color 15 (Grey) { %color = 15 | mymsg %color } - } alias mymsg { if ($1 == 00) { echo -a * Color: 00 - White } if ($1 == 01) { echo -a * Color: 01 - Black } if ($1 == 02) { echo -a * Color: 02 - Navy } if ($1 == 03) { echo -a * Color: 03 - Green } if ($1 == 04) { echo -a * Color: 04 - Red } if ($1 == 05) { echo -a * Color: 05 - Brown } if ($1 == 06) { echo -a * Color: 06 - Purple } if ($1 == 07) { echo -a * Color: 07 - Orange } if ($1 == 08) { echo -a * Color: 08 - Yellow } if ($1 == 09) { echo -a * Color: 09 - Light Green } if ($1 == 10) { echo -a * Color: 10 - Teal } if ($1 == 11) { echo -a * Color: 11 - Light Blue } if ($1 == 12) { echo -a * Color: 12 - Blue } if ($1 == 13) { echo -a * Color: 13 - Pink } if ($1 == 14) { echo -a * Color: 14 - Dark Grey } if ($1 == 15) { echo -a * Color: 15 - Grey } } #talker off on *:input:*:{ if (/* !iswm $1) { var %c = $+($chr(3),%color,$1-,$chr(3)) !msg $target $iif(c isincs $chan($target).mode,$strip(%c),%c) halt } } #talker end ; Color Talker v1.1 - by entropy 2018 ; Only use this script on channels where you are chan op! (or you might get banned) menu channel { - Color Talker $chr(9) $+([,$iif($group(#talker).status == on,On,Off),]) .Turn $iif($group(#talker).status == on,Off,On) { $iif($group(#talker).status == on,.disable,.enable) #talker | echo -a * Color Talker is now: $iif($group(#talker).status == on,On,Off) } .- .Color $chr(9) $+([,%color,]) ..Color 00 (White) { %color = 00 | mymsg %color } ..Color 01 (Black) { %color = 01 | mymsg %color } ..Color 02 (Navy) { %color = 02 | mymsg %color } ..Color 03 (Green) { %color = 03 | mymsg %color } ..Color 04 (Red) { %color = 04 | mymsg %color } ..Color 05 (Brown) { %color = 05 | mymsg %color } ..Color 06 (Purple) { %color = 06 | mymsg %color } ..Color 07 (Orange) { %color = 07 | mymsg %color } ..Color 08 (Yellow) { %color = 08 | mymsg %color } ..Color 09 (Light Green) { %color = 09 | mymsg %color } ..Color 10 (Teal) { %color = 10 | mymsg %color } ..Color 11 (Light Blue) { %color = 11 | mymsg %color } ..Color 12 (Blue) { %color = 12 | mymsg %color } ..Color 13 (Pink) { %color = 13 | mymsg %color } ..Color 14 (Dark Grey) { %color = 14 | mymsg %color } ..Color 15 (Grey) { %color = 15 | mymsg %color } - } alias mymsg { if ($1 == 00) { echo -a * Color: 00 - White } if ($1 == 01) { echo -a * Color: 01 - Black } if ($1 == 02) { echo -a * Color: 02 - Navy } if ($1 == 03) { echo -a * Color: 03 - Green } if ($1 == 04) { echo -a * Color: 04 - Red } if ($1 == 05) { echo -a * Color: 05 - Brown } if ($1 == 06) { echo -a * Color: 06 - Purple } if ($1 == 07) { echo -a * Color: 07 - Orange } if ($1 == 08) { echo -a * Color: 08 - Yellow } if ($1 == 09) { echo -a * Color: 09 - Light Green } if ($1 == 10) { echo -a * Color: 10 - Teal } if ($1 == 11) { echo -a * Color: 11 - Light Blue } if ($1 == 12) { echo -a * Color: 12 - Blue } if ($1 == 13) { echo -a * Color: 13 - Pink } if ($1 == 14) { echo -a * Color: 14 - Dark Grey } if ($1 == 15) { echo -a * Color: 15 - Grey } } #talker off on *:input:*:{ if (/* !iswm $1) { var %c = $+($chr(3),%color,$1-,$chr(3)) !msg $target $iif(c isincs $chan($target).mode,$strip(%c),%c) halt } } #talker end Clipboard
-
/* ** mIRC Automated Execution Script v1.1.0 ** ** Author: Sierra Brown [ SierraKomodo ] ** Website: https://gist.github.com/SierraKomodo/18c877055a49629758260d0690bc9ba6 ** IRC: SierraKomodo @ irc.freenode.net ** ** Provides some better control over automated functions to occur when you start mirc, connect to a ** server, or join a channel. Everything is stored into separated .ini files stored in ** scripts/config by default (Change the global variable %glo.ConfigPath to set a new location - ** Make sure the folder exists.) ** ** Refer to the example entries in the autoconnect, autocommand, and autojoin ini files. ** ** Implemented features: ** * Auto connect on start, including delayed autoconnections, support for multiple servers, and ** full support for most features of the /server command ** * Auto join on connection to server, including delayed auto joins and support for channel keys ** * Auto command on connection to server, allowing executing any IRC commands - Essentially runs ** /raw command here */ ; INI file paths alias -l locGlobalConfig return $+(%glo.ConfigPath, autoexec.ini) alias -l locGlobalConfig.AutoConnect return $+(%glo.ConfigPath, autoexec-autoconnect.ini) alias -l locServerConfig return $+(%glo.ConfigPath, $network, /autoexec.ini) alias -l locServerConfig.AutoJoin return $+(%glo.ConfigPath, $network, /autoexec-autojoin.ini) alias -l locServerConfig.AutoCommand return $+(%glo.ConfigPath, $network, /autoexec-autocommand.ini) alias -l locChannelConfig return $+(%glo.ConfigPath, $iif($2, $2, $network), /, $iif($1, $1, $chan), /autoexec.ini) alias -l locError return $+(%glo.ConfigPath, error.log) on *:START: { if (%glo.ConfigPath == $null) { mkdir scripts mkdir scripts/config var -g %glo.ConfigPath = scripts/config/ } ; Write default config entries/generate files if ($readini($locGlobalConfig, n, Config, bAutoConnect) == $null) { writeini $locGlobalConfig Config bAutoConnect 0 } if ($readini($locGlobalConfig, n, Config, iAutoConnectDelay) == $null) { writeini $locGlobalConfig Config iAutoConnectDelay 5 } if ($readini($locGlobalConfig, n, Config, sAutoConnectList) == $null) { writeini $locGlobalConfig Config sAutoConnectList ExampleServer writeini $locGlobalConfig.AutoConnect ExampleServer sAddress irc.example.com writeini $locGlobalConfig.AutoConnect ExampleServer iPort 6667 writeini $locGlobalConfig.AutoConnect ExampleServer sPassword Password writeini $locGlobalConfig.AutoConnect ExampleServer bSSL 0 writeini $locGlobalConfig.AutoConnect ExampleServer sNick Nickname writeini $locGlobalConfig.AutoConnect ExampleServer sAltNick Alternate Nickname writeini $locGlobalConfig.AutoConnect ExampleServer sRealName Real Name writeini $locGlobalConfig.AutoConnect ExampleServer sIdent Ident writeini $locGlobalConfig.AutoConnect ExampleServer iDelay 5 } ; Auto Connect if (($readini($locGlobalConfig, n, Config, bAutoConnect)) && ($readini($locGlobalConfig, n, Config, sAutoConnectList) != $null)) { ; If autoconnect global delay is set, delay auto connection by X seconds - This delay exists to allow mIRC to load up fully before executing connections. if ($readini($locGlobalConfig, n, Config, iAutoConnectDelay) > 0) { timerglo.AutoConnect -o 1 $v1 atimer.AutoConnect } else { atimer.AutoConnect } } } on *:CONNECT: { if (!$exists(%glo.ConfigPath $+ $network)) { mkdir %glo.ConfigPath $+ $network } ; Write default config entries/generate files if ($readini($locServerConfig, n, Config, bAutoJoin) == $null) { writeini $locServerConfig Config bAutoJoin 0 } if ($readini($locServerConfig, n, Config, iAutoJoinDelay) == $null) { writeini $locServerConfig Config iAutoJoinDelay 3 } if ($readini($locServerConfig, n, Config, sAutoJoinList) == $null) { writeini $locServerConfig Config sAutoJoinList #Example writeini $locServerConfig.AutoJoin #Example sKey Password writeini $locServerConfig.AutoJoin #Example iDelay 5 } if ($readini($locServerConfig, n, Config, bAutoCommand) == $null) { writeini $locServerConfig Config bAutoCommand 0 } if ($readini($locServerConfig, n, Config, iAutoCommandDelay) == $null) { writeini $locServerConfig Config iAutoCommandDelay 1 } if ($readini($locServerConfig, n, Config, sAutoCommandList) == $null) { writeini $locServerConfig Config sAutoCommandList ExampleCommand writeini $locServerConfig.AutoCommand ExampleCommand 1 privmsg NickServ identify password writeini $locServerConfig.AutoCommand ExampleCommand 2 other command to send to the server } ; Auto Join if (($readini($locServerConfig, n, Config, bAutoJoin)) && ($readini($locServerConfig, n, Config, sAutoJoinList) != $null)) { ; If autojoin global delay is set, delay auto join by X seconds - This delay exists to allow mIRC to finish processing any on CONNECT scripts before executing joins. if ($readini($locServerConfig, n, Config, iAutoJoinDelay) > 0) { timer [ $+ [ $cid ] $+ ] .AutoJoin 1 $v1 atimer.AutoJoin } else { atimer.AutoJoin } } ; Auto Command if (($readini($locServerConfig, n, config, bAutoCommand)) && ($readini($locServerConfig, n, Config, sAutoCommandList) != $null)) { ; If autocommand delay is set, delay commands by X seconds - This delay exists to allow mIRC to finish processing any on CONNECT scripts before executing any other commands if ($readini($locServerConfig, n, Config, iAutoCommandDelay) > 0) { timer [ $+ [ $cid ] $+ ] .AutoCommand 1 $v1 atimer.AutoCommand } else { atimer.AutoCommand } } } alias atimer.AutoConnect { ; Cycle through each server name entry in [Config] sAutoConnectList var %loc.AutoConnectList = $readini($locGlobalConfig, n, Config, sAutoConnectList) var %loc.NewWindow = 0 var %loc.Count = 1 while (%loc.Count <= $gettok(%loc.AutoConnectList, 0, 32)) { var %loc.Current = $gettok(%loc.AutoConnectList, %loc.Count, 32) ; Check if the server name provided exists in the autoconnect ini file if ($readini($locGlobalConfig.AutoConnect, n, %loc.Current, sAddress) != $null) { var %loc.Address = $v1 var %loc.Port = $iif($readini($locGlobalConfig.AutoConnect, n, %loc.Current, iPort) != $null, $v1, 6667) var %loc.Password = $readini($locGlobalConfig.AutoConnect, n, %loc.Current, sPassword) var %loc.SSL = $iif($readini($locGlobalConfig.AutoConnect, n, %loc.Current, bSSL) != $null, $v1, 0) var %loc.Nick = $readini($locGlobalConfig.AutoConnect, n, %loc.Current, sNick) var %loc.AltNick = $iif($readini($locGlobalConfig.AutoConnect, n, %loc.Current, sAltNick), $v1, $+(%loc.Nick, _)) var %loc.RealName = $iif($readini($locGlobalConfig.AutoConnect, n, %loc.Current, sRealName), $v1, mIRC $version) var %loc.Ident = $iif($readini($locGlobalConfig.AutoConnect, n, %loc.Current, sIdent), $v1, mirc) var %loc.Delay = $readini($locGlobalConfig.AutoConnect, n, %loc.Current, iDelay) ; Connect to the server if (%loc.Delay != $null) { if (%loc.Nick != $null) { timerglo.AutoConnect. [ $+ [ %loc.Current ] ] -o 1 %loc.Delay server $iif(%loc.NewWindow, -m) %loc.Address $iif(%loc.SSL, $+(+, %loc.Port), %loc.Port) %loc.Password -i %loc.Nick %loc.AltNick $+(%loc.Ident, @fake-ident-email.com)) %loc.RealName } else { timerglo.AutoConnect. [ $+ [ %loc.Current ] ] -o 1 %loc.Delay server $iif(%loc.NewWindow, -m) %loc.Address $iif(%loc.SSL, $+(+, %loc.Port), %loc.Port) %loc.Password } } else { if (%loc.Nick != $null) { server $iif(%loc.NewWindow, -m) %loc.Address $iif(%loc.SSL, $+(+, %loc.Port), %loc.Port) %loc.Password -i %loc.Nick %loc.AltNick $+(%loc.Ident, @fake-ident-email.com)) %loc.RealName } else { server $iif(%loc.NewWindow, -m) %loc.Address $iif(%loc.SSL, $+(+, %loc.Port), %loc.Port) %loc.Password } } ; Set the 'New Window' flag to open all future server connections in a new connection window. if (%loc.NewWindow == 0) %loc.NewWindow = 1 unset %loc.Address %loc.Port %loc.Password %loc.SSL %loc.Nick %loc.AltNick %loc.RealName %loc.Ident } ; Go to next entry unset %loc.Current inc %loc.Count continue :error echo -a * AutoExec Error in atimer.AutoConnect %loc.Current : $error write $locError $logstamp - AutoExec Error in atimer.AutoConnect %loc.Current : $error unset %loc.Current ; reseterror inc %loc.Count continue } return :error echo -a * AutoExec Error in atimer.AutoConnect : $error write $locError $logstamp - AutoExec Error in atimer.AutoConnect : $error ; reseterror } alias atimer.AutoJoin { ; Cycle through each channel entry in [Config] sAutoJoinList var %loc.AutoJoinList = $readini($locServerConfig, n, Config, sAutoJoinList) var %loc.Count = 1 while (%loc.Count <= $gettok(%loc.AutoJoinList, 0, 32)) { var %loc.Current = $gettok(%loc.AutoJoinList, %loc.Count, 32) ; Check if already in channel if ($me !ison %loc.Current) { var %loc.Key = $readini($locServerConfig.AutoJoin, n, %loc.Current, sKey) var %loc.Delay = $readini($locGlobalConfig.AutoJoin, n, %loc.Current, iDelay) ; Join the channel if (%loc.Delay != $null) { timer [ $+ [ $cid ] $+ ] .AutoJoin. [ $+ [ %loc.Current ] ] join %loc.Current %loc.Key } else { join %loc.Current %loc.Key } } ; Go to next entry inc %loc.Count continue :error echo -a * AutoExec Error in atimer.AutoJoin %loc.Current ( CID: $cid ) : $error write $locError $logstamp - AutoExec Error in atimer.AutoJoin %loc.Current ( CID: $cid ) : $error ; reseterror inc %loc.Count continue } return :error echo -a * AutoExec Error in atimer.AutoJoin ( CID: $cid ) : $error write $locError $logstamp - AutoExec Error in atimer.AutoJoin ( CID: $cid ) : $error ; reseterror } alias atimer.AutoCommand { ; Cycle through each command entry in [Config] sAutoCommandList var %loc.AutoCommandList = $readini($locServerConfig, n, Config, sAutoCommandList) var %loc.Count = 1 while (%loc.Count <= $gettok(%loc.AutoCommandList, 0, 32)) { var %loc.Current = $gettok(%loc.AutoCommandList, %loc.Count, 32) ; Loop through each command line var %loc.Count2 = 1 while ($readini($locServerConfig.AutoCommand, n, %loc.Current, %loc.Count2) != $null) { raw $readini($locServerConfig.AutoCommand, n, %loc.Current, %loc.Count2) inc %loc.Count2 continue :error echo -a * AutoExec Error in atimer.AutoCommand %loc.Current entry %loc.Count2 ( CID: $cid ) : $error write $locError $logstamp - AutoExec Error in atimer.AutoCommand %loc.Current entry %loc.Count2 ( CID: $cid ) : $error ; reseterror inc %loc.Count2 continue } inc %loc.Count continue :error echo -a * AutoExec Error in atimer.AutoCommand %loc.Current ( CID: $cid ) : $error write $locError $logstamp - AutoExec Error in atimer.AutoCommand %loc.Current ( CID: $cid ) : $error ; reseterror inc %loc.Count continue } return :error echo -a * AutoExec Error in atimer.AutoCommand ( CID: $cid ) : $error write $locError $logstamp - AutoExec Error in atimer.AutoCommand ( CID: $cid ) : $error ; reseterror }
-
on *:TEXT:*:#: { if (($nick !isop $chan) && ($me isop $chan)) { if ($mhighlightcheck($chan,$1-) > 5) { ban -k $chan $nick 3 [AutoKick] Mass Highlight. } } } alias mhighlightcheck { ;$1 chan ;$2 text ;returns number of highlighted nicks ; var %count = 0, %x = 1, %text = $replace($strip($2-),$chr(44),$chr(32)) while ($numtok(%text,32) > 0) { if ($gettok(%text,%x,32) ison $1) { inc %count } else { } var %text $remtok(%text,$v1,0,32) } return %count
-
; Whois mods by Sebastien (xplo) ; $comchan alias from someone in a help chan somewhere. ; If you touch at something below this line, you WILL fuckup something. ; Example: http://i.imgur.com/tLi75RP.png ; /w nick alias w { .enable #whois | whois $1 $1 } #whois off raw 311:*: { echo $color(notice) -ai2 14[7###14] $iif($me == $2,Looking at yourself?,/whois7 $2) echo -ai2 2Nick:14 $2 echo -ai2 2Address:14 $3 $+ @ $+ $4 echo -ai2 2FullName:14 $6- halt } raw 379:*:{ echo -ai2 2Is using modes:14 $6- | halt } raw 378:*:{ echo -ai2 2Is Connecting from:14 $6- | halt } raw 319:*: { echo -ai2 2Channels:4 $sorttok($3-,32,c) $iif($2 == $me,halt,echo -ai2 2Common Channels:11 $AdoComChan($2)) halt } raw 312:*: { echo -ai2 2Server:14 $3 echo -ai2 2Description:14 $4- halt } raw 330:*:{ echo -ai2 2Username: 4 $+ $3 $+ | halt } raw 338:*:{ echo -ai2 2Host:14 $3 | halt } raw 307:*:{ echo -ai2 3 $+ $2 $3- | halt } raw 301:*:{ echo -ai2 2 $+ $2 is away:7 $3- | halt } raw 313:*:{ echo -ai2 2Status:14 $5- | halt } raw 310:*:{ echo -ai2 2 $+ $2 14 $+ $3- | halt } raw 320:*:{ echo -ai2 2 $+ $2 14 Is using a Secure Connection (4SSL14) | halt } raw 335:*:{ echo -ai2 2 $+ $2 14 Is a Bot on $network (4BOT14) | halt } raw 671:*:{ echo -ai2 2 $+ $2 14 Is using a Secure Connection (4SSL14) | halt } raw 317:*:{ echo -a 2Idle time:4 $duration($3) if ($4 isnum) echo -ai2 2Online time:14 $asctime($4) halt } raw 318:*:{ echo $color(notice) -ai2 14[7###14] End of Whois for7 $2 linesep -a .disable #whois halt } alias AdoComChan { var %AdoComCh = 1 while (%AdoComCh <= $comchan($1,0)) { var %AdoComLi = %AdoComLi $comchan($1,%AdoComCh) inc %AdoComCh } if (%AdoComLi == $null) { return None } else { return %AdoComLi } } #whois end #EOF
-
; Script to display whois information in an @window ; - Ook ; ; All the whois raws are captured but only the nick, address, idle, server, channels info is shown ; with a little tinkering more can easily be added. ; ; v1.0 ; - First release ; v1.1 ; - fixed possible error in endofwhois when $address fails. ; - added some more error output. ; - changed tabs to cut off text that exceeds limits. ; - changed code to update horiz scrollbar on end of whois (doesnt display whole line still, this is mircs fault) ; - channel name no longer needed, will take active window as channel if no channel name given. ; ; /whoischan <chan> ; $1 = chan alias whoischan { if ($0 > 1) { echo -aqmlbfti2 [whoischan] Usage: /whoischan <#channel> | halt } var %i = 1, %c = $iif($0,$1,$active) window -lM -t20,100,130,170 @whoischan clear @whoischan aline @whoischan $+( Nick,$chr(9),Address,$chr(9),Idle Time,$chr(9),Server,$chr(9),Channels) aline @whoischan while ($nick(%c,%i) != $null) { var %n = $v1 aline @whoischan $+(%n,$chr(9),$iif($address(%n,5) != $null,$v1,unknown),$chr(9),0,$chr(9),-,$chr(9),$chr(160)) _pushwhois %n %n inc %i } !return :error !echo 4 -s whoischan: $error } alias -l _nnet { !if ($network != $null) return $v1 !elseif ($server($server).group != $null) { !if ($v1 !isnum) return $v1 } !return Default :error !echo 4 -s _nnet: $error } ; start temp data hashtable functs ; $1 = var (delete temp var) alias -l tdel !if ($hget(whoischan)) hdel whoischan $1 ; $1 = var wildcard (del temp vars that matcvh wildcard) alias -l twdel !if ($hget(whoischan)) hdel -w whoischan $1 ; $1 = var, $2- = data (add a temp var) alias -l tadd !hadd whoischan $1- ; $1 = var (get the contents of a temp var) alias -l tget !return $hget(whoischan,$1-) ; end temp data hashtable functs alias -l _pushwhois { !var %cid = $cid !hadd -m $+(%cid,-whois-queue) $1 $1- if (!$timer($+(%cid,-pushwhois))) $+(.timer,%cid,-pushwhois) 1 0 _pushwhois.dump !return :error !echo 4 -s _pushwhois: $error } alias -l _pushwhois.dump { !var %cid = $cid, %limit = $tget($+(%cid,-maxtarget-WHOIS)) !if (!%limit) var %limit = 1 !if ($tget($+(%cid,enable_combined_whois))) { ; if the network supports it combine the /whois into one !while ($hget($+(%cid,-whois-queue),1).data != $null) { !var %n = $v1 !if ($numtok(%n,32) == 1) { ; single nick /whois nick style, these can be combined. !var %whois = $addtok(%whois,%n,44) !hdel $+(%cid,-whois-queue) $hget($+(%cid,-whois-queue),1).item !if ($numtok(%whois,44) == %limit) break } ; otherwise its /whois nick nick style, these can't be combined. !elseif (%whois != $null) break !else { !var %whois = %n !hdel $+(%cid,-whois-queue) $hget($+(%cid,-whois-queue),1).item !break } !inc %cnt } } !else { ; otherwise do a single whois & pause before next !var %whois = $hget($+(%cid,-whois-queue),1).data !hdel $+(%cid,-whois-queue) $hget($+(%cid,-whois-queue),1).item } if ($hget($+(%cid,-whois-queue),0).item > 0) $+(.timer,%cid,-pushwhois) 1 2 _pushwhois.dump else hfree $+(%cid,-whois-queue) if (%whois != $null) whois %whois !return :error !echo 4 -s _pushwhois.dump: $error } RAW 5:*: { !if ($hget(whoischan) == $null) hmake whoischan 100 !var %cid = $cid, %tmp = $matchtokcs($1-,SILENCE,1,32) if (%tmp) tadd $+(%cid,-silence) $gettok(%tmp,2,61) else tadd $+(%cid,-silence) 0 !var %tmp = $matchtokcs($1-,TOPICLEN,1,32) if (%tmp) tadd $+(%cid,-topiclen) $gettok(%tmp,2,61) else tadd $+(%cid,-topiclen) 0 !var %tmp = $matchtokcs($1-,NICKLEN,1,32) if (%tmp) tadd $+(%cid,-nicklen) $gettok(%tmp,2,61) else tadd $+(%cid,-nicklen) 0 !var %tmp = $matchtokcs($1-,UHNAMES,1,32) if (%tmp) tadd $+(%cid,-uhnames) 1 else tadd $+(%cid,-uhnames) 0 !var %tmp = $matchtokcs($1-,TARGMAX,1,32) !if (%tmp) { !var %cnt = 1, %tmp = $gettok(%tmp,2,61) !while ($gettok(%tmp,%cnt,44) != $null) { tadd $+(%cid,-maxtarget-,$gettok($v1,1,58)) $gettok($v1,2,58) !inc %cnt } } else twdel $+(%cid,-maxtarget-*) !var %tmp = $matchtokcs($1-,MAXLIST,1,32) !if (%tmp) { !var %cnt = 1, %tmp = $gettok(%tmp,2,61) !while ($gettok(%tmp,%cnt,44) != $null) { !var %t = $+(%cid,-maxlist-,$gettok($v1,1,58)) tadd %t $gettok($v1,2,58) if ($tget(%t) == $null) tadd %t 1 !inc %cnt } } else twdel $+(%cid,-maxlist-*) !var %tmp = $matchtokcs($1-,AWAYLEN,1,32) if (%tmp) tadd $+(%cid,-awaylen) $gettok(%tmp,2,61) else tadd $+(%cid,-awaylen) 0 !var %tmp = $matchtokcs($1-,KICKLEN,1,32) if (%tmp) tadd $+(%cid,-kicklen) $gettok(%tmp,2,61) else tadd $+(%cid,-kicklen) 0 !var %nnet = $_nnet !if ($istok(DALnet UnderNet BeyondIRC IRCHighway SwiftIRC Genscripts,%nnet,32)) { ; net supports combined whois tadd $+(%cid,enable_combined_whois) 1 !if ($tget($+(%cid,-maxtarget-WHOIS)) == $null) { ; max targets wasn't set for some reason, try a known value for that network. if (%nnet == Undernet) tadd $+(%cid,-maxtarget-WHOIS) 12 elseif (%nnet == Genscripts) tadd $+(%cid,-maxtarget-WHOIS) 20 else tadd $+(%cid,-maxtarget-WHOIS) 4 } } else tdel $+(%cid,enable_combined_whois) } ; output line = nick address idle-time server channels ;275 HighwayIRC RPL_WHOISSECURE "<TheirNick> is using a secure connection (SSL)" raw 275:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;301 RPL_AWAY "<nick> :<away message>" raw 301:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;307 DALnet RPL_WHOISREGNICK Registered Nick “:<nick> is a registered nick raw 307:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;308 DALnet RPL_WHOISADMIN Server Admin (may be dropped) raw 308:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;309 DALnet RPL_WHOISSADMIN Services Admin (may be dropped) “: <nick> is a services adminstrator raw 309:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;310 DALnet RPL_WHOISHELPOP "%s :looks very helpful.", “<nick> <help status msg>" - A sample reply is: “White_Dragon looks very helpful.” raw 310:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;311 RPL_WHOISUSER "<nick> <user> <host> * :<real name>" - The '*' in RPL_WHOISUSER is there as the literal character and not as a wild card raw 311:*: { !if ($fline(@whoischan,$+($2,$chr(9),*),1,1) != $null) { var %l = $v1 haltdef rline @whoischan %l $puttok($line(@whoischan,%l),$chr(160),5,9) } } ;312 RPL_WHOISSERVER "<nick> <server> :<server info>" raw 312:*: { ;echo -s whoischan312: $1- !if ($fline(@whoischan,$+($2,$chr(9),*),1,1) != $null) { var %l = $v1 haltdef rline @whoischan %l $puttok($line(@whoischan,%l),$chr(160) $3,4,9) } } ;313 RPL_WHOISOPERATOR "<nick> :is an IRC operator" raw 313:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;316 RPL_WHOISCHANOP raw 316:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;317 RPL_WHOISIDLE "<nick> <integer> :seconds idle" raw 317:*: { ;echo -s whoischan317: $1- !if ($fline(@whoischan,$+($2,$chr(9),*),1,1) != $null) { var %l = $v1 haltdef rline @whoischan %l $puttok($line(@whoischan,%l),$chr(160) $duration($3),3,9) } } ;318 RPL_ENDOFWHOIS "<nick>(,nick,nick,...) :End of /WHOIS list" raw 318:*: { ;echo -s whoischan318: $1- !var %i = 1 !while ($gettok($2,%i,44) != $null) { !var %n = $v1 !if ($fline(@whoischan,$+(%n,$chr(9),*),1,1) != $null) { var %l = $v1 haltdef if ($address(%n,5) != $null) rline @whoischan %l $puttok($line(@whoischan,%l),$chr(160) $v1,2,9) } inc %i } } ;319 RPL_WHOISCHANNELS "<nick> :{[@|+]<channel><space>}" raw 319:*: { !if ($fline(@whoischan,$+($2,$chr(9),*),1,1) != $null) { var %l = $v1 haltdef var %txt = $line(@whoischan,%l) rline @whoischan %l $puttok(%txt,$addtok($gettok(%txt,5,9),$3-,32),5,9) window -b @whoischan } } ;330 Undernet/Quakenet RPL_WHOISACCOUNT "<source> 330 <target> <nick> <account> :is authed as" returned when using the WHOIS command on UnderNet "is logged in as" is shown as text raw 330:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;335 RPL_WHOISBOT raw 335:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;338 RPL_WHOISACTUALLY ":%s 338 %s :%s is actually %s@%s [%s]" raw 338:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;615 HighwayIRC RPL_WHOISMODES "<TheirNick> is using modes <modes>" raw 615:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef ;616 HighwayIRC RPL_WHOISREALHOST "<TheirNick> real hostname <host> <ip>" raw 616:*: !if ($fline(@whoischan,$+($2,$chr(9),*),0,1) != $null) haltdef